Baltimore IMC : http://www.baltimoreimc.org
Commentary :: Elections & Legislation
Brazil: The Perfect Electoral Crime (II)
Security Failures in the electronic voting machines (DRE's) in the US and in Brazil.
Brazil: The Perfect Electoral Crime (II)
Security Failures in the electronic voting machines (DRE's) in the US and in Brazil.
Notice: The author of this article acts as the technical representative of some political parties in relations to the federal Elections Division (loose translation of "Justiça Eleitoral", the Tribunal Superior Eleitoral -TSE) in Brazil, which operates all elections, where he has had access to information about the internal project of the Brazilian electronic voting machines. For this, he was obliged to sign an agreement of secrecy such that he cannot divulge information which he received from within that official agency. Thus, this report on the Brazilian DRE's presented here are only those which can be obtained in documents and in public proceedings such as Resolutions and Instructions of the Tribunal Superior Eleitoral (TSE), the technical parameters (specifications) included in the RFP's (Requests for Proposals) bidding documents asking for supply of the DRE's, the official technical reports presented by academic units (UNICAMP, SBC e COPPE-UFRJ), technical articles by others presented in conventions and the internet, the participation in public ceremonies of loading, testing and sealing of the DRE's, records of public processes and judicial investigations.
1- Introduction:
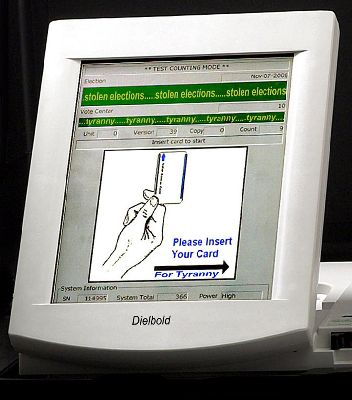
On May 11, 2006, the non-profit organization Black Box Voting (BBV) made public the second part of a report by the information systems specialist Harri Hursti, containing analysis and free tests developed in relation to the electronic voting machines (DRE's) models TSx, manufactured by the company Diebold and sold in the USA and in Canada, where they cover about 30% of those markets.
These types of tests of independent attack are technically called "Penetration Tests" and the Hursti Reports (1st and 2nd Parts) may be obtained at:
www.blackboxvoting.org/BBVreport.pdf
www.blackboxvoting.org/BBVtsxstudy.pdf
The basic conclusion of these reports is that there exist security failures in the design and manufacture of these Diebold DREs' used in the US and Canada, which permit that the voting program can be adulterated to modify the results in the counting of the votes.
The first part of the Hursti Report, in December 2005, described how it was possible to adulterate the programs in the Diebold DRE'S actually used in Leon County, Florida, in such a way to fraudulently affect the voting. The immediate consequence of the publishing of this report was the firing of the President of Diebold which, until that moment, continued to say that it was impossible to fraudulently affect their DRE's.
The repercussion of the seconf report, in the American press, was rapid and intense, as can be seen in:
- The New York Times
www.nytimes.com/2006/05/12/us/12vote.html
- The Register
www.theregister.com/2006/05/14/diebold_e-voting_flaw/
- The Beacon Journal
www.ohio.com/mld/beaconjournal/business/14561489.htm
As the company Diebold holds almost 90% of the Brazilian market of DRE's, where under the brand-name Diebold-Procomp it produced 375 thousand of the 426 thousand DRE's which will be utilized in the Brazilian Presidential elections in October of 2006, it is necessary to analyze whether the security failures pointed out in the Hursti Reports also exist in the DRE models furnished in Brazil.
2- The Hursti Analysis - Part 2:
The second part of the Hursti Report was developed regarding the DRE's Diebold models TSx and TS6, supplied to the Emery County in the state of Utah. It made public with almost 50 places censored (replaced by the expression "redacted") by those responsible at BBV, in virtue of information content which, by chance, might facilitate the improper use of the information by third parties in future elections.
The report concludes with the existence of grave security breaches which permit the adulteration of the voting programs in such a way as to fraudulently affect a future election.
The spokespersons for the factory are defending themselves, affirming that:
a) there is no proof that fraud has occurred in regular elections;
b) the vulnabilities found are "theoretical" and with a very low probability of being actually exploited;
and the "pearl" of the tattered excuses where David Bear, a spokesman for Diebold Election Systems, said (in the NY Times):
c) "For there to be a problem here, you're basically assuming a premise where you have some evil and nefarious election officials who would sneak in and introduce a piece of software. I don't believe these evil elections people exist."
It might seem trivial to state that a computer program can be adulterated for malicious purposes, but the analysis by Mr Hursti is high;y rigorous and complete, affirming in addition to this, that the security breaches in the Diebold DRE's:
a) Permit that the alterations which are possible may not only alter votes, but also fool the verification integrity tests regularly used by election simulations and the verifications of the digital signatures "Hash";
b) the possibility of modifying the programs were introduced by Diebold, in part, intentionally by the programmers to facilitate the tasks of updating the software;
c) They permit modifications of the programs on three levels of control (boot system, operating system, and application programs), in such a way that the changes may even carry over to future updates, automatically recontaminating the machines.
The possibility of modifications to the DRE's would not be a grave problem if they contained some way to have the final vote-counting audited. For example, the paper ballot verified by the voter produced by the DRE's Model SAE3000 of the company Smartmatic, which were used in the elections of 2004 and 2005 in Venezuela, permit the auditing of the electronic vote-counting and, if there were adukteration of the voting programs, the fraud could have been detected.
However, the Diebold machines, both those available in the USA and in Brazil, do not furnish this alternative way to verify the votes, so the confidence in the software is everything which guarantees a correct election result.
Thus, if in these machines the software can be modified without the knowledge or consent of the manufacturer, whatever possibility of affirming the confidence in the equipment falls to the ground.
Among the security failures in the model TSx of Diebold are:
a) the boot-system may be modified by software;
b) it is possible to modify the internal programs by external digital methods;
c) the OS (Windows CE) does not possess strong resources of security;
d) the system of physical seals is insufficient and the case is easy to open, without destroying anything;
e) it is possible to reconfigure the security resources by means of jumpers on the motherboard;
f) there exists an internal socket for multimedia memory cards;
g) the external button labelled "battery test" can be used for attacks set off by a voter;
resulting in the requirement of less than 5 minutes to contaminate a previously healthy machine.
3- The Brazilian DRE models:
The models (98, 2000, 2002, 2004 and 2006) of the Brazilian DRE's are totally controlled by the technical staff of the TSE, in such a way that the 51 thousand furnished by Unisys (model 2002) and the 375 thousand furnished by Diebold (the other models) possess exactly the same characteristics of operation, usability and safety.
Different from the US TSx models which, for the interaction of the voter, they have an integrated screen and "keyboard" (touch-screen), the Brazilian models have separate fixed numerical keyboard and a LCD screen and are of the design patented by their first creator, Engineer Carlos Rocha.
The models 98 e 2000, which represent 2/3 of the DRE's, use the OS VirtuOS, similar to the old DOS complemented with multi-tasking, and the later models have the same Windows CE of the american TSx.
For standardization of the interface with the voter, and since the VirtuOS has very limited visual resources, all the Brazilian DRE's work with the screen totally in text format (DOS-like) without using the resources of the graphic interface of Windows.
This impossibility to configure the screen as a "keyboard" (touch-screen) is what provoked the difficulties during the vote of the Referendum of 2005, because the fixed keyboard did not have keys labelled "YES" and "NO" which were needed.
4- The security characteristics of the Braziliam DRE's:
In Brazil, the TSE (federal elections division) combines the duties of inspection, and administration of the election process and the power of the judge for all election material resources, even those which are contrary its administrative acts. Due to human nature, this accumulation of powers, which are not found in mature democratic regimes, naturally lead to authoritarianism and lack of transparency. Because of this, official requests for Security Penetration Tests presented repeated times by some political parties have been systematically blocked by this elections super-organ by the simple fact that it had the power to centralize the decision and impede such tests.
Thus, there are no reports in Brazil similar to the Hursti Reports, but it is still possible to discover the fragilities of the Brazilian DRE's by the analysis of the official documents published as the technical specifications in supply bidding for the furnishing of the machines, and the statements of technical expertise found within some jusicial processes.
In this way, it can be affirmed that the security (and insecurity) resources of the Brazilian DRE's are similar, when compared to that described in the Hursti Report on the Diebold TSx model.
a) they do not create a printed vote verified by the voter which permits an audit of the vote-counting, so that they are highly dependent on the trusting of the software;
b) They have a BIOS chip (with boot function) installed in a socket and re-recordable by software, as specified in the bidding specifications;
c) they have a "BIOS extension" accomplished by a "jumper" on the motherboard (information obtained from the inspection of the DRE's used in the re-registration of the City of Camaçari, Bahia, Brazil, where the BIOS-extension was disactivated, see [CHA-02]) which permitted the boot from the external socket from an external flash-card memory;
d) It is possible to execute "batch file" software recorded on a diskette, as described in the Unicamp Report [UNI-02] ;
e) the application program which verifies the internal integrity of the system is itself extremely vulnerable to adulterations [REZ-04];
f) the system of seals and closure of the box are simple and permit access to the socket of the internal memory cartridge, as described in the inspection report in the City of Sto. Estevão, Bahia, Brazil [REG-04];
This set of characteristics of (in)security of the Brazilian DRE's make them just as subject to fraud as their American similar models.
The possibility of booting (starting operation) of the Brazilian DRE's by using a memory-card inserted in the external socket, is an enormous security fault, since the program which commands the boot can do, fololowing that, whatever it is programmed to do - including changes to the internal software previously installed. But this resource was established on purpose by the system programmers, in order to more easily do the program upgrades in the DRE's, as has been learned by analyzing the (public) procedures for loading and re-loading the software, as seen here:
i) Normal procedure for loading the machines.
This is done by way of a loading Flash-card, which is located on the external connector of the machine. Upon powering up the machine with this memory device installed, one can see that the boot is done via the drive D: (the external connector for the Flash-card), which then copies all the official software to the internal memory of the DREs.
During this installation, everything which was in the machine is erased, except for (beginning in 2004) the archive of the log of the previous booting of the same system.
In this log archive, a record is made of the new boot information, done by the loading program itself, (which is loaded on the external Flash-card) as can be deduced from the following Item (ii). After loading, the external Flash-card is replaced by another without a boot system in such a way that during an election and voting, the boot operation is controlled by the software installed on the internal flash-card.
ii) Exceptional procedure for loading the machines used in 2002:
In 2002, the voting software used during the first session presented intermittent faults which led to modifications for the voting in the second session. The installation of this new software was done differently from the normal installation. A new flash-card was prepared and, when placed in the external socket of the DRE's, only exchanged the defective voting software with the new version, "preserving" all the other data and archives stored on the internal flash-card during the first session, and placing in the log archive some events different from the normal loading program.
Note: the quote-marks on the word "preserving" were used because, naturally, the external inspectors did not have any way to know if the previous data were being preserved, or not, especially after the case of the "Hash Dance" exposed by a member of the "Forum of E-Voting", when it was discovered that there were differences between the "hash" signatures of the system finally installed in the machines and that which was presented to the Inspectors at the headquarters of the TSE (Federal Tribunal for Elections) before the new loading.
These two procedures, norma and exceptional, of loading the Brazilian DRE's demonstrates that it is perfectly possible to install complete or partial software on the DRE's by the use of an external flash-card suitable prepared, and furthermore, that the log archive is totally controlled by the same method from the external flash-card.
Worse yet, this same external software, which gets passed onto the internal flash-card which controls the machine during voting, during the tally and, notably, even during the digital signature tests permitted by the external inspectors.
In other words, a "well-prepared" program installed by external flash-card can break through both the counting of the votes and the tests of machine reliability also.
5 - Conclusions
The similarities between the security faults of the DRE's made by Diebold in the US and Brazil, which depend on the security of the software but which permit that this software can be adulterated by external agents, seems more than a simple coincidence.
In Brazil a positive image of the DRE's has been developed, in spite of those responsible not permitting any audits of the vote-counting.
The security resources applied here, even not being sufficient from the point of view strictly techically, were sufficient to convince the ordinary voters with the official publications repeated insistently that it utilized "advanced technological resources of digital signatures and cryptography". The lay public did not really understand what this served for, but believed the claims that the electronic voting machines "are 100% secure" and that "we have eliminated election fraud".
Diebold knew success until the moment of this social experience, where security resources were used not with efficacy but only as a means of illusory publicity. It is natural that they would attempt the same "strategy" in the US.
But the existence of a central agency with super-powers like the Brazilian National Electoral Justice agency (TSE) seems to be creating difficulties with the strategy which was applied here.
In Brasil, the TSE managed, from 2000 until today (2006), block, by way of obscure and authoritarian decisions, that there could be made any type of free analasis of its DRE machines, such as that done by Mr Hursti, and it continues hiding from the inattentive voters, the fragilities of its electronic voting system.
6- References:
[CHA-02] - www.votoseguro.org/textos/camacari1.htm resumo - www.votoseguro.org/arquivos/camacari1.zip
[UNI-02] - www.tse.gov.br/eleicoes/seguranca/relatorio_unicamp/rel_final.zip resumo - www.votoseguro.org/textos/relfuncamp1.htm
[REZ-04] - www.cic.unb.br/docentes/pedro/trabs/analise_setup.html
[REG-04] - www.votoseguro.org/arquivos/stoestevao.zip resumo - www.votoseguro.org/textos/stoestevao1.htm
------------------------
s/
Amilcar Brunazo Filho
www.votoseguro.org
I KNOW WHO I VOTED FOR
THEY ALSO KNOW
BUT ONLY THEY KNOW WHO RECEIVED MY VOTE
Security Failures in the electronic voting machines (DRE's) in the US and in Brazil.
Notice: The author of this article acts as the technical representative of some political parties in relations to the federal Elections Division (loose translation of "Justiça Eleitoral", the Tribunal Superior Eleitoral -TSE) in Brazil, which operates all elections, where he has had access to information about the internal project of the Brazilian electronic voting machines. For this, he was obliged to sign an agreement of secrecy such that he cannot divulge information which he received from within that official agency. Thus, this report on the Brazilian DRE's presented here are only those which can be obtained in documents and in public proceedings such as Resolutions and Instructions of the Tribunal Superior Eleitoral (TSE), the technical parameters (specifications) included in the RFP's (Requests for Proposals) bidding documents asking for supply of the DRE's, the official technical reports presented by academic units (UNICAMP, SBC e COPPE-UFRJ), technical articles by others presented in conventions and the internet, the participation in public ceremonies of loading, testing and sealing of the DRE's, records of public processes and judicial investigations.
1- Introduction:
On May 11, 2006, the non-profit organization Black Box Voting (BBV) made public the second part of a report by the information systems specialist Harri Hursti, containing analysis and free tests developed in relation to the electronic voting machines (DRE's) models TSx, manufactured by the company Diebold and sold in the USA and in Canada, where they cover about 30% of those markets.
These types of tests of independent attack are technically called "Penetration Tests" and the Hursti Reports (1st and 2nd Parts) may be obtained at:
www.blackboxvoting.org/BBVreport.pdf
www.blackboxvoting.org/BBVtsxstudy.pdf
The basic conclusion of these reports is that there exist security failures in the design and manufacture of these Diebold DREs' used in the US and Canada, which permit that the voting program can be adulterated to modify the results in the counting of the votes.
The first part of the Hursti Report, in December 2005, described how it was possible to adulterate the programs in the Diebold DRE'S actually used in Leon County, Florida, in such a way to fraudulently affect the voting. The immediate consequence of the publishing of this report was the firing of the President of Diebold which, until that moment, continued to say that it was impossible to fraudulently affect their DRE's.
The repercussion of the seconf report, in the American press, was rapid and intense, as can be seen in:
- The New York Times
www.nytimes.com/2006/05/12/us/12vote.html
- The Register
www.theregister.com/2006/05/14/diebold_e-voting_flaw/
- The Beacon Journal
www.ohio.com/mld/beaconjournal/business/14561489.htm
As the company Diebold holds almost 90% of the Brazilian market of DRE's, where under the brand-name Diebold-Procomp it produced 375 thousand of the 426 thousand DRE's which will be utilized in the Brazilian Presidential elections in October of 2006, it is necessary to analyze whether the security failures pointed out in the Hursti Reports also exist in the DRE models furnished in Brazil.
2- The Hursti Analysis - Part 2:
The second part of the Hursti Report was developed regarding the DRE's Diebold models TSx and TS6, supplied to the Emery County in the state of Utah. It made public with almost 50 places censored (replaced by the expression "redacted") by those responsible at BBV, in virtue of information content which, by chance, might facilitate the improper use of the information by third parties in future elections.
The report concludes with the existence of grave security breaches which permit the adulteration of the voting programs in such a way as to fraudulently affect a future election.
The spokespersons for the factory are defending themselves, affirming that:
a) there is no proof that fraud has occurred in regular elections;
b) the vulnabilities found are "theoretical" and with a very low probability of being actually exploited;
and the "pearl" of the tattered excuses where David Bear, a spokesman for Diebold Election Systems, said (in the NY Times):
c) "For there to be a problem here, you're basically assuming a premise where you have some evil and nefarious election officials who would sneak in and introduce a piece of software. I don't believe these evil elections people exist."
It might seem trivial to state that a computer program can be adulterated for malicious purposes, but the analysis by Mr Hursti is high;y rigorous and complete, affirming in addition to this, that the security breaches in the Diebold DRE's:
a) Permit that the alterations which are possible may not only alter votes, but also fool the verification integrity tests regularly used by election simulations and the verifications of the digital signatures "Hash";
b) the possibility of modifying the programs were introduced by Diebold, in part, intentionally by the programmers to facilitate the tasks of updating the software;
c) They permit modifications of the programs on three levels of control (boot system, operating system, and application programs), in such a way that the changes may even carry over to future updates, automatically recontaminating the machines.
The possibility of modifications to the DRE's would not be a grave problem if they contained some way to have the final vote-counting audited. For example, the paper ballot verified by the voter produced by the DRE's Model SAE3000 of the company Smartmatic, which were used in the elections of 2004 and 2005 in Venezuela, permit the auditing of the electronic vote-counting and, if there were adukteration of the voting programs, the fraud could have been detected.
However, the Diebold machines, both those available in the USA and in Brazil, do not furnish this alternative way to verify the votes, so the confidence in the software is everything which guarantees a correct election result.
Thus, if in these machines the software can be modified without the knowledge or consent of the manufacturer, whatever possibility of affirming the confidence in the equipment falls to the ground.
Among the security failures in the model TSx of Diebold are:
a) the boot-system may be modified by software;
b) it is possible to modify the internal programs by external digital methods;
c) the OS (Windows CE) does not possess strong resources of security;
d) the system of physical seals is insufficient and the case is easy to open, without destroying anything;
e) it is possible to reconfigure the security resources by means of jumpers on the motherboard;
f) there exists an internal socket for multimedia memory cards;
g) the external button labelled "battery test" can be used for attacks set off by a voter;
resulting in the requirement of less than 5 minutes to contaminate a previously healthy machine.
3- The Brazilian DRE models:
The models (98, 2000, 2002, 2004 and 2006) of the Brazilian DRE's are totally controlled by the technical staff of the TSE, in such a way that the 51 thousand furnished by Unisys (model 2002) and the 375 thousand furnished by Diebold (the other models) possess exactly the same characteristics of operation, usability and safety.
Different from the US TSx models which, for the interaction of the voter, they have an integrated screen and "keyboard" (touch-screen), the Brazilian models have separate fixed numerical keyboard and a LCD screen and are of the design patented by their first creator, Engineer Carlos Rocha.
The models 98 e 2000, which represent 2/3 of the DRE's, use the OS VirtuOS, similar to the old DOS complemented with multi-tasking, and the later models have the same Windows CE of the american TSx.
For standardization of the interface with the voter, and since the VirtuOS has very limited visual resources, all the Brazilian DRE's work with the screen totally in text format (DOS-like) without using the resources of the graphic interface of Windows.
This impossibility to configure the screen as a "keyboard" (touch-screen) is what provoked the difficulties during the vote of the Referendum of 2005, because the fixed keyboard did not have keys labelled "YES" and "NO" which were needed.
4- The security characteristics of the Braziliam DRE's:
In Brazil, the TSE (federal elections division) combines the duties of inspection, and administration of the election process and the power of the judge for all election material resources, even those which are contrary its administrative acts. Due to human nature, this accumulation of powers, which are not found in mature democratic regimes, naturally lead to authoritarianism and lack of transparency. Because of this, official requests for Security Penetration Tests presented repeated times by some political parties have been systematically blocked by this elections super-organ by the simple fact that it had the power to centralize the decision and impede such tests.
Thus, there are no reports in Brazil similar to the Hursti Reports, but it is still possible to discover the fragilities of the Brazilian DRE's by the analysis of the official documents published as the technical specifications in supply bidding for the furnishing of the machines, and the statements of technical expertise found within some jusicial processes.
In this way, it can be affirmed that the security (and insecurity) resources of the Brazilian DRE's are similar, when compared to that described in the Hursti Report on the Diebold TSx model.
a) they do not create a printed vote verified by the voter which permits an audit of the vote-counting, so that they are highly dependent on the trusting of the software;
b) They have a BIOS chip (with boot function) installed in a socket and re-recordable by software, as specified in the bidding specifications;
c) they have a "BIOS extension" accomplished by a "jumper" on the motherboard (information obtained from the inspection of the DRE's used in the re-registration of the City of Camaçari, Bahia, Brazil, where the BIOS-extension was disactivated, see [CHA-02]) which permitted the boot from the external socket from an external flash-card memory;
d) It is possible to execute "batch file" software recorded on a diskette, as described in the Unicamp Report [UNI-02] ;
e) the application program which verifies the internal integrity of the system is itself extremely vulnerable to adulterations [REZ-04];
f) the system of seals and closure of the box are simple and permit access to the socket of the internal memory cartridge, as described in the inspection report in the City of Sto. Estevão, Bahia, Brazil [REG-04];
This set of characteristics of (in)security of the Brazilian DRE's make them just as subject to fraud as their American similar models.
The possibility of booting (starting operation) of the Brazilian DRE's by using a memory-card inserted in the external socket, is an enormous security fault, since the program which commands the boot can do, fololowing that, whatever it is programmed to do - including changes to the internal software previously installed. But this resource was established on purpose by the system programmers, in order to more easily do the program upgrades in the DRE's, as has been learned by analyzing the (public) procedures for loading and re-loading the software, as seen here:
i) Normal procedure for loading the machines.
This is done by way of a loading Flash-card, which is located on the external connector of the machine. Upon powering up the machine with this memory device installed, one can see that the boot is done via the drive D: (the external connector for the Flash-card), which then copies all the official software to the internal memory of the DREs.
During this installation, everything which was in the machine is erased, except for (beginning in 2004) the archive of the log of the previous booting of the same system.
In this log archive, a record is made of the new boot information, done by the loading program itself, (which is loaded on the external Flash-card) as can be deduced from the following Item (ii). After loading, the external Flash-card is replaced by another without a boot system in such a way that during an election and voting, the boot operation is controlled by the software installed on the internal flash-card.
ii) Exceptional procedure for loading the machines used in 2002:
In 2002, the voting software used during the first session presented intermittent faults which led to modifications for the voting in the second session. The installation of this new software was done differently from the normal installation. A new flash-card was prepared and, when placed in the external socket of the DRE's, only exchanged the defective voting software with the new version, "preserving" all the other data and archives stored on the internal flash-card during the first session, and placing in the log archive some events different from the normal loading program.
Note: the quote-marks on the word "preserving" were used because, naturally, the external inspectors did not have any way to know if the previous data were being preserved, or not, especially after the case of the "Hash Dance" exposed by a member of the "Forum of E-Voting", when it was discovered that there were differences between the "hash" signatures of the system finally installed in the machines and that which was presented to the Inspectors at the headquarters of the TSE (Federal Tribunal for Elections) before the new loading.
These two procedures, norma and exceptional, of loading the Brazilian DRE's demonstrates that it is perfectly possible to install complete or partial software on the DRE's by the use of an external flash-card suitable prepared, and furthermore, that the log archive is totally controlled by the same method from the external flash-card.
Worse yet, this same external software, which gets passed onto the internal flash-card which controls the machine during voting, during the tally and, notably, even during the digital signature tests permitted by the external inspectors.
In other words, a "well-prepared" program installed by external flash-card can break through both the counting of the votes and the tests of machine reliability also.
5 - Conclusions
The similarities between the security faults of the DRE's made by Diebold in the US and Brazil, which depend on the security of the software but which permit that this software can be adulterated by external agents, seems more than a simple coincidence.
In Brazil a positive image of the DRE's has been developed, in spite of those responsible not permitting any audits of the vote-counting.
The security resources applied here, even not being sufficient from the point of view strictly techically, were sufficient to convince the ordinary voters with the official publications repeated insistently that it utilized "advanced technological resources of digital signatures and cryptography". The lay public did not really understand what this served for, but believed the claims that the electronic voting machines "are 100% secure" and that "we have eliminated election fraud".
Diebold knew success until the moment of this social experience, where security resources were used not with efficacy but only as a means of illusory publicity. It is natural that they would attempt the same "strategy" in the US.
But the existence of a central agency with super-powers like the Brazilian National Electoral Justice agency (TSE) seems to be creating difficulties with the strategy which was applied here.
In Brasil, the TSE managed, from 2000 until today (2006), block, by way of obscure and authoritarian decisions, that there could be made any type of free analasis of its DRE machines, such as that done by Mr Hursti, and it continues hiding from the inattentive voters, the fragilities of its electronic voting system.
6- References:
[CHA-02] - www.votoseguro.org/textos/camacari1.htm resumo - www.votoseguro.org/arquivos/camacari1.zip
[UNI-02] - www.tse.gov.br/eleicoes/seguranca/relatorio_unicamp/rel_final.zip resumo - www.votoseguro.org/textos/relfuncamp1.htm
[REZ-04] - www.cic.unb.br/docentes/pedro/trabs/analise_setup.html
[REG-04] - www.votoseguro.org/arquivos/stoestevao.zip resumo - www.votoseguro.org/textos/stoestevao1.htm
------------------------
s/
Amilcar Brunazo Filho
www.votoseguro.org
I KNOW WHO I VOTED FOR
THEY ALSO KNOW
BUT ONLY THEY KNOW WHO RECEIVED MY VOTE
Views
Information
Search
This site made manifest by dadaIMC software